Screen Door on a Submarine
Last week, a class-action lawsuit alleged that Perplexity AI shares the full text of user prompts with Meta and Google via hidden tracking scripts.[1] The prompts travel even when Incognito mode is enabled. The privacy setting controls what Perplexity saves. It does not control what Meta and Google receive.
The response, predictably, was advice. Use a VPN. Clear your cookies. Switch browsers. Enable Do Not Track. The advice is well-meaning. It is also useless.
A VPN hides your IP address. The tracking scripts do not use your IP address. They use your browser fingerprint: screen resolution, GPU model, installed fonts, timezone, language settings, hardware concurrency, canvas rendering patterns.[2] A VPN changes where you appear to be. It does not change who you are.
Clearing cookies removes one tracking mechanism. Browser fingerprinting does not use cookies. It reads the hardware and software configuration of your device, which does not change when you clear a cache. The fingerprint persists because you persist. Your machine is your identity.
Do Not Track is a request header. It asks websites not to track you. No major advertising network honours it.[3] Jonathan Mayer, a professor at Princeton University who helped draft the original DNT specification, called it "a failed experiment in self-regulation."[4] It is a polite note left on the door of a house that has already been burgled.
The question is not which setting to toggle. The question is whether the architecture of the tool permits privacy at all.

Francisco Goya, "Saturn Devouring His Son" (1820-23). Museo del Prado, Madrid. The system that consumes the people it was built to serve. Public domain.
What TOR Actually Does
The Tor Browser is the closest thing to real anonymity available in a standard web browser.[5] It works by routing your traffic through three encrypted relays, each of which knows only the relay before it and the relay after it. No single node in the chain knows both who you are and where you are going. The exit node sees the destination but not the origin. Your ISP sees that you are using Tor but not what you are doing.
More importantly for the Perplexity problem: Tor blocks the tracking scripts.
Tor Browser disables or sandboxes JavaScript by default in its safest mode. It standardizes the browser fingerprint so that every Tor user looks identical to every other Tor user – same screen size (via letterboxing), same reported timezone (UTC), same font list, same canvas rendering.[6] A Meta Pixel running inside a Tor session cannot fingerprint the user because there is nothing unique to fingerprint. The script runs in a standardized environment that returns the same values for every visitor.
The Electronic Frontier Foundation's Cover Your Tracks tool, which tests browser fingerprint uniqueness, reports that Tor Browser with its default settings produces a fingerprint shared by hundreds of thousands of users.[7] Chrome in Incognito mode produces a fingerprint that is unique to the individual device.
Incognito mode hides your history from the person sitting next to you. Tor hides your identity from the company sitting inside the page.
There are costs. Tor is slow. The multi-relay architecture adds latency. Many websites block Tor exit nodes or present CAPTCHAs. Some AI services refuse connections from known Tor IP ranges. Using Perplexity through Tor may not work at all, which is itself an answer: the service is architecturally incompatible with anonymity.
What TOR Does Not Do
Network identity is what Tor protects. It does not protect the content of your conversation.
When you use Perplexity through Tor, the tracking scripts cannot fingerprint you. Meta and Google receive a standardized, anonymous browser profile. Your IP is hidden. Your device is unidentifiable. This is meaningful protection against surveillance and ad targeting.
The prompt still goes to Perplexity. Perplexity still sends it to the underlying model provider (OpenAI or Anthropic). The content of your question (your family's medical situation, your legal exposure, your financial strategy) still travels to servers you do not control, processed by companies whose terms of service you accepted by clicking a button.
As Bruce Schneier, security technologist and fellow at the Berkman Klein Center for Internet & Society at Harvard, has written: "Privacy is about controlling who has access to information about you."[8] Tor controls who sees your network traffic. It does not control who processes your prompt.
For that, you need a different architecture entirely.
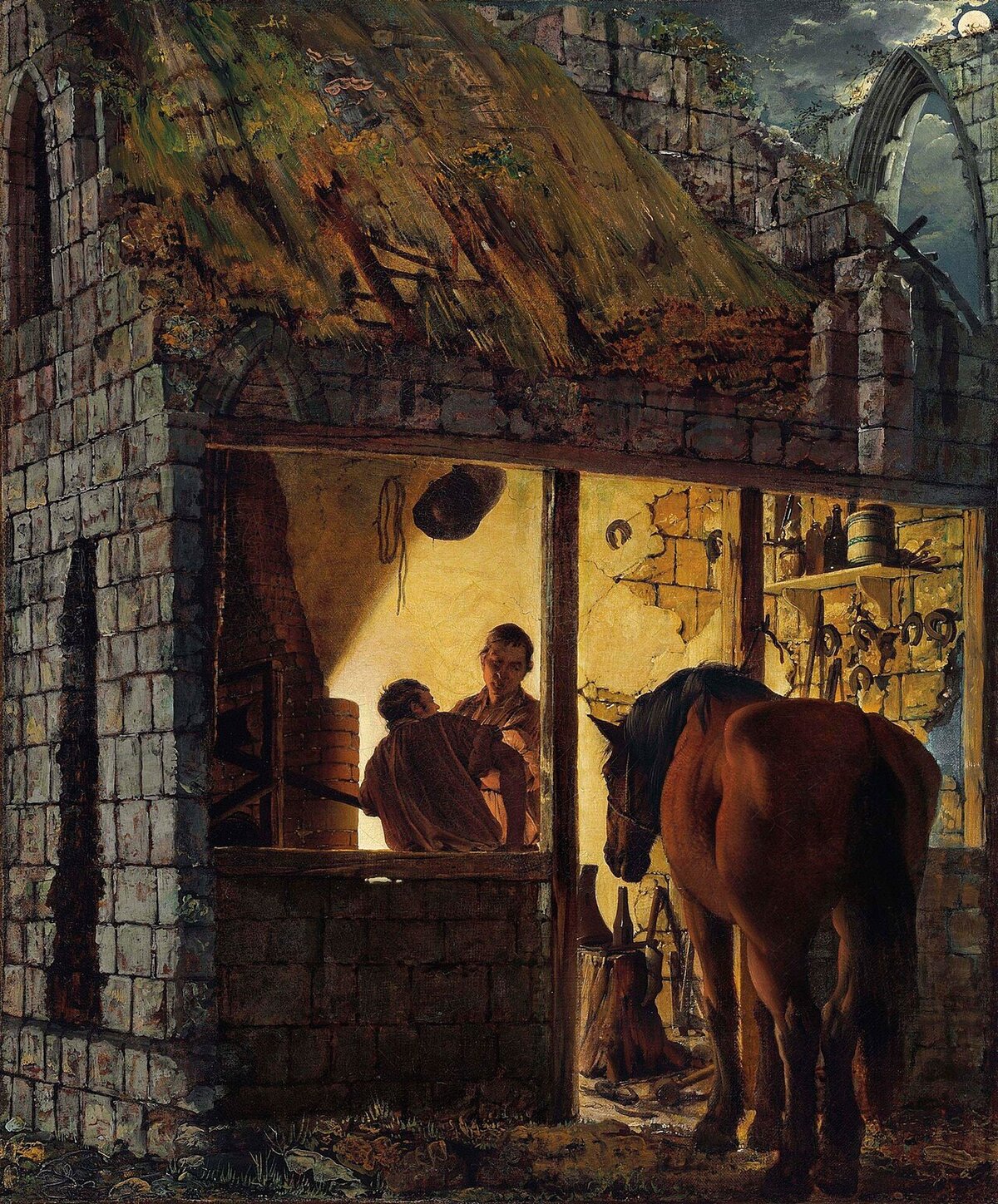
Joseph Wright of Derby, "A Blacksmith's Shop" (1771). Yale Center for British Art. The forge is owned by the smith. The tools are his. The fire is his. The work stays in the building. Public domain.
The Only Private Conversation
There is exactly one architecture in which a conversation with an AI is genuinely private: the AI runs on your hardware, the interface runs on your server, and no network request carrying your prompt leaves the building.
This is not theoretical. It is a product category.
Ollama runs open-weight language models on a local machine.[9] Open WebUI provides a browser-based interface that connects to Ollama without transmitting data to any external server. Perplexica, an open-source project, replicates Perplexity's web-search functionality using SearXNG (an anonymous meta-search engine) feeding results into a local model.[10] Every search stays on your hardware. No tracking scripts. No Meta Pixel. No Google Analytics. No prompt leaves the machine.
DeepSeek-R1-Distill-Qwen3-8B runs advanced reasoning on an 8-billion-parameter model that fits on a laptop GPU.[11] The reasoning capability that required an OpenAI API subscription eighteen months ago now runs offline, air-gapped, with zero network exposure. The most private conversation you can have with an AI is one where the AI has no internet connection.
The trade-off is real. Local models trail the frontier in capability. They lack Perplexity's web-search integration, ChatGPT's plugin ecosystem, Claude's context window. For many tasks, the managed cloud is faster, more capable, and more convenient. The question is whether the task involves information you would not type into a search engine owned by an advertising company – because that is what you are doing when you use Perplexity with tracking scripts active.
The most private AI is the one that cannot phone home. Not because it promised not to. Because the network cable is unplugged.
The Middle Ground That Actually Works
Most people will not run a local LLM. Most organizations will not air-gap their AI infrastructure. The practical question is whether a middle ground exists between "your prompts go to three companies" and "your AI runs on a laptop in a Faraday cage."
It does. Self-hosted AI platforms connect to cloud models (Claude, GPT, Gemini, DeepSeek) through an interface the organization controls. The model provider receives the prompt – that is what an API does. But the platform itself contains no tracking scripts, no advertising SDK, no Meta Pixel, no Google Analytics. The conversation stays between you and the model provider. Two parties instead of four.
Sage.is AI-UI operates on this architecture. AGPL-3 licensed, self-hostable, model-agnostic.[12] No tracking scripts – the code is open and verifiable. No third-party analytics. Conversations are stored on the organization's infrastructure, exportable as structured data, never transmitted to advertising networks. When the sensitivity of the task demands it, the same interface connects to a self-hosted model, reducing the parties involved to one: you.
Sage does not replicate Perplexity's web-search pipeline or ChatGPT's consumer feature set.[13] It is a workspace, not a search engine. The architecture is the argument: you can use frontier models without embedding advertising infrastructure in the conversation.
The Stack That Actually Protects You
Here is what each layer does and does not do:
Tor Browser blocks tracking scripts, prevents fingerprinting, hides your IP. It does not protect the content of your prompt from the service you send it to. Use it when you need anonymity on the network.
A VPN hides your IP from your ISP and the destination server. It does not prevent fingerprinting, does not block tracking scripts, and does not protect prompt content. It is one layer, not a solution.
Browser privacy settings (Firefox strict mode, Brave shields) block known trackers and reduce fingerprint surface. They do not eliminate fingerprinting and do not protect prompt content. Better than nothing. Not enough.
Self-hosted AI platform (Sage, Open WebUI + Ollama) eliminates tracking scripts from the conversation interface. When connected to a cloud model, the prompt goes to one party (the model provider) instead of three. When connected to a local model, the prompt goes nowhere.
Local-only AI (Ollama, Jan, GPT4All with no network) is the only fully private option. The prompt never leaves the machine. Zero parties receive your data. The trade-off is capability.
The combination that provides both capability and privacy: Tor for browsing, self-hosted AI for thinking. Your web activity is anonymous. Your AI conversations are sovereign. No advertising company receives either.
The Architecture Is the Activism
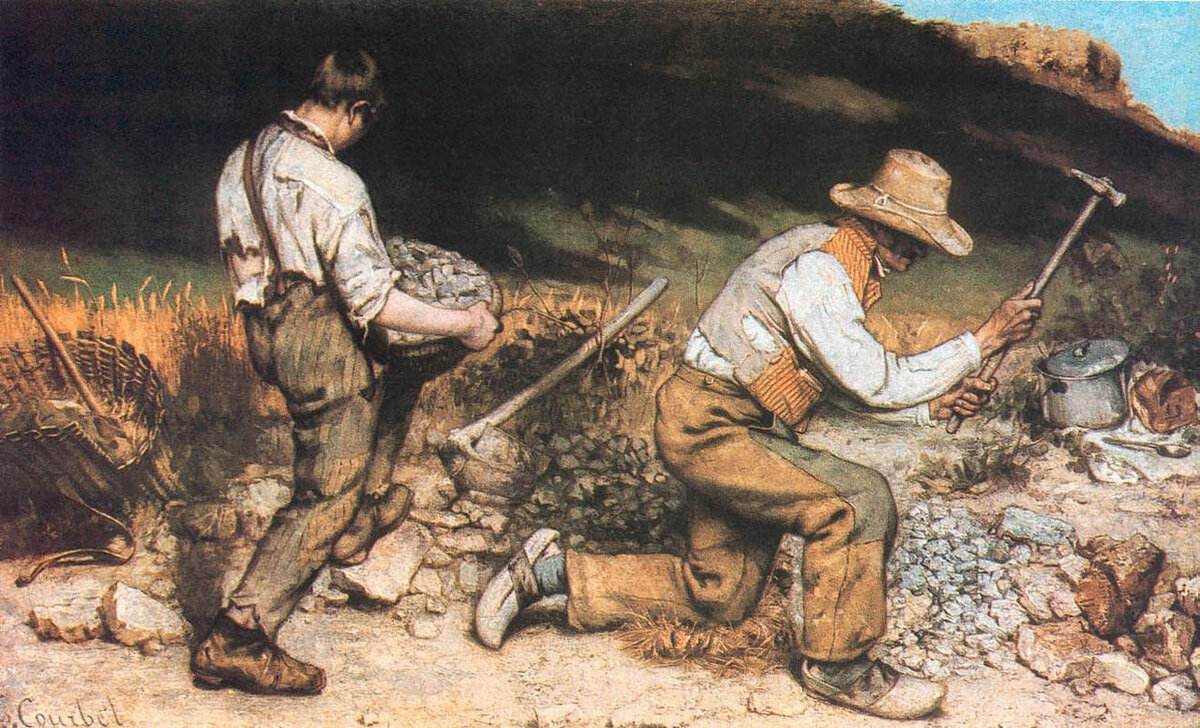
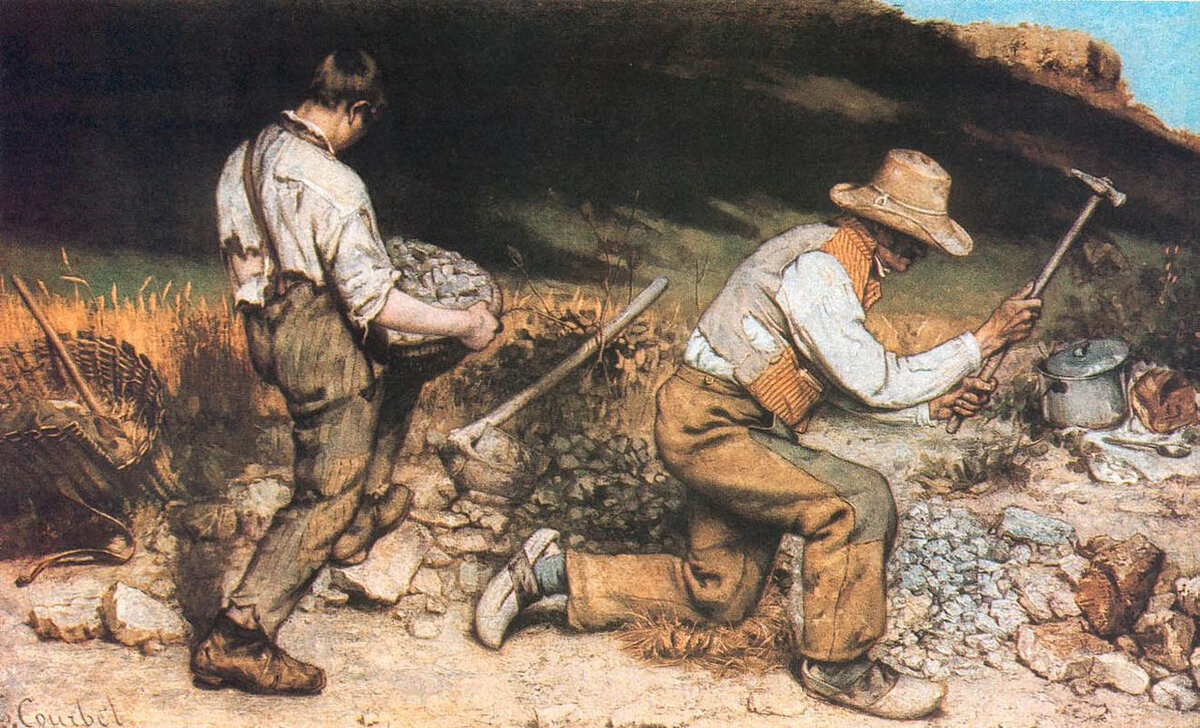
Gustave Courbet, "The Stone Breakers" (1849). The painting that founded Realism — art that showed the world as it was, not as institutions wanted it seen. Destroyed in the bombing of Dresden, 1945. Known only from reproductions. Public domain.
Google reversed its opposition to browser fingerprinting in February 2025.[14] What the industry once treated as a privacy violation became, overnight, an accepted practice. The companies that build browsers, run search engines, and operate advertising networks are the same companies. The referee and the player wear the same jersey.
The EFF, the Tor Project, the open-source community, and the self-hosting movement are not fighting a technical battle. They are fighting an economic one. Every prompt typed into an advertising-funded AI platform generates revenue for the advertising network. Every prompt typed into a self-hosted platform generates nothing for anyone except the person who typed it. The business model is the surveillance. The architecture is the resistance.
Perplexity's Incognito mode is a screen door on a submarine. It gives you the feeling of privacy while the hull is open to the ocean. The fix is not a better screen door. The fix is a different vessel.
Run Tor when you browse. Run your own AI when you think. Own the infrastructure that processes your most sensitive questions. The tools exist. The models exist. The only thing that does not exist is the expectation that privacy requires building something, not just toggling something.
The prompt you thought was private can be private. It requires architecture, not settings.
The views expressed are those of the editorial board. Sage.is AI-UI is a product of Startr LLC. The author has no financial relationship with Perplexity AI, Meta, Google, or the Tor Project. Full disclosure and transparency is a feature, not a bug.
Class-action lawsuit filed April 1, 2026, U.S. District Court, Northern District of California. Perplexity AI Inc., Meta Platforms Inc., Alphabet Inc./Google. Bloomberg. ↩︎
Browser fingerprinting uses hardware and software configuration to identify users without cookies. ML models now process fingerprint data in milliseconds. Hackaday, "Browser Fingerprinting And Why VPNs Won't Make You Anonymous". See also: AI-Driven Browser Fingerprinting. ↩︎
Do Not Track was proposed as a standard by the FTC in 2010. No major advertising network honours it. The W3C Tracking Protection Working Group was closed in 2019 without achieving compliance. ↩︎
Jonathan Mayer, Princeton University. Mayer co-authored the original Do Not Track specification and has published extensively on its failure as a self-regulatory mechanism. ↩︎
Tor Project. torproject.org. Multi-relay onion routing with end-to-end encryption between relays. ↩︎
Tor Browser fingerprinting protections: letterboxing, timezone normalization (UTC), font list standardization, canvas rendering uniformity. Tor Browser features. ↩︎
Electronic Frontier Foundation, Cover Your Tracks. coveryourtracks.eff.org. Tests browser fingerprint uniqueness and tracking protection. ↩︎
Bruce Schneier, Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World (W.W. Norton, 2015). Schneier is a fellow at the Berkman Klein Center for Internet & Society, Harvard University. ↩︎
Ollama. ollama.com. Local LLM runner supporting Llama, Mistral, DeepSeek, Qwen, and other open-weight models. ↩︎
Perplexica, open-source Perplexity alternative using SearXNG + local LLM. XDA Developers. ↩︎
DeepSeek-R1-Distill-Qwen3-8B, released May 2025. Advanced reasoning distilled into 8B parameters. Runs on consumer GPU hardware. ↩︎
Sage.is AI-UI, AGPL-3 licensed. sage.is. Self-hostable, model-agnostic, no tracking scripts, no third-party analytics. ↩︎
Sage is a workspace platform, not a web-search engine. It does not replicate Perplexity's crawling/indexing pipeline or ChatGPT's consumer plugin ecosystem. ↩︎
Google reversed opposition to browser fingerprinting, February 2025. Reported by Hackaday and URTech. ↩︎
 Sage.is
Sage.is